As technology continues to develop, there’s also an increase in the number of potential risks and threats to businesses. Businesses that store data must also be able to protect it. This article lists 2 ways that encryption can help achieve this.
What is Encryption?
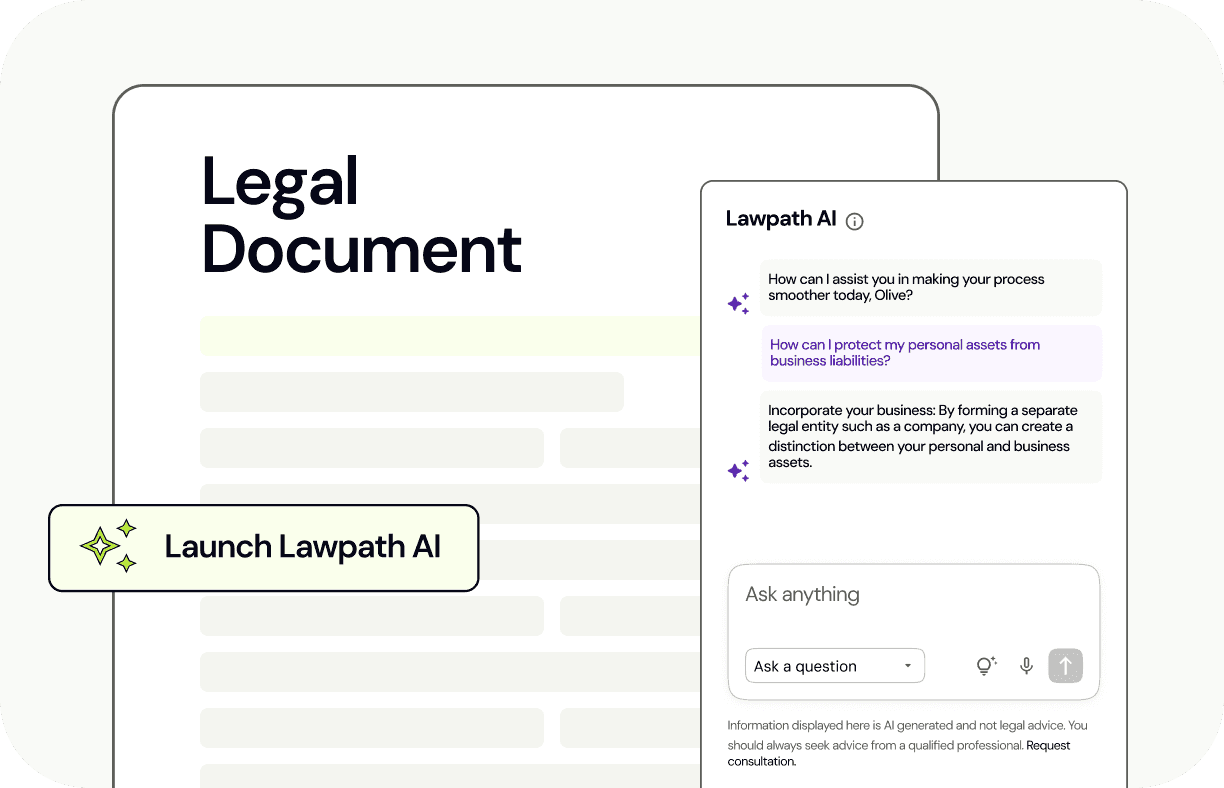
Encryption converts data into code so that only the people who have the required key can decode it. The rest of this article explains symmetric and asymmetric encryption, which are the main methods of encryption.
Symmetric Encryption
This method is simple but effective. Data that is ‘at rest’, whether it is sitting on a device or in the cloud can benefit from this security measure. A key encrypts and decrypts the data, with only the user having access to that key. If a business only requires one person to access sensitive data, this method of protection is ideal.
Asymmetric Encryption
If symmetric encryption is not suitable for your business’ needs, here is an alternative. This method involves a pair of related keys called public and private keys, where the private key is secret. Multiple parties can then encrypt data using the public key whereas only the holder of the private key can decrypt it. Businesses with many parties who need to access sensitive information can use this method to securely communicate while protecting data. In addition to asymmetric encryption, it is important to authenticate users accessing the sensitive information. There must also be restrictions on users who can access protected data so only the bare minimum of users can access it. This is to avoid a similar situation to Bupa last year. If your business is in need of a document which informs your customers about how their personal information is collected and used, refer to our Privacy Policy.
Potential Changes in Australian Law
The Telecommunications and Other Legislation Amendment (Assistance and Access) Bill 2018 which was introduced on 20 September 2018 has received criticism from a wide range of tech giants and telecommunications companies. The legislation’s purpose is to assist law enforcement bodies intercept encrypted messages between individuals engaged in criminal activities. The bill can force telecommunications companies or device manufacturers to modify products. This is so the government can decode encrypted messages. However, this also makes it possible for hackers to exploit weaknesses in the device for criminal purposes.
In a world where cyber security threats are becoming more prominent, it is important to protect your customers’ data. While we have discussed one method to do this, a Privacy Lawyer can advise you as to what other methods you can use to ensure your business is protected.
Have more questions? Contact a LawPath consultant on 1800 529 728 to learn more about customising legal documents and obtaining a fixed-fee quote from Australia’s largest legal marketplace.